Endpoint and Authentication:
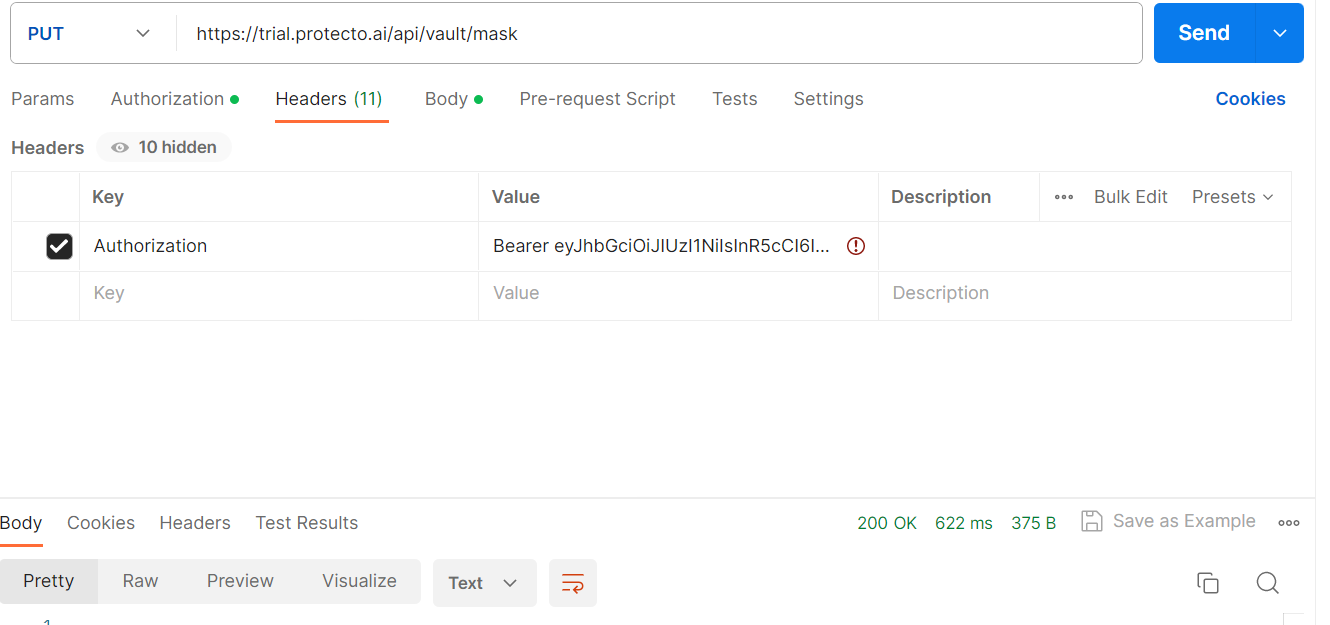
To use Protecto.ai’s token-based masking, you need to send a PUT request to the following endpoint:
Endpoint: https://trail.protecto.ai/api/vault/unmask
For authentication, include the following token in the request headers:
Headers: {“Authorization”: “Bearer <AUTH_TOKEN>”}
Request Payload:
Here’s an example of a request payload to unmask data:
{"unmask":[{"token_value":"8oGEcGVEkj 700ZSgo1pA"}]}
token_value(string): The token for which the original value needs to be retrieved.
{
"data": [
{
"token_value": "8oGEcGVEkj 700ZSgo1pA",
"value": "George Williams"
}
],
"success": true,
"error": {
"message": ""
}
}
- token_value (string): The original token that was provided in the request.
- value (string): The original sensitive data value retrieved from the token.
Advantage :
Authorized Data Access: Unmasking allows authorized personnel to access the original, unmasked data when needed, while still keeping the data protected during other stages of processing or storage.
Note : Unmasking should be performed under strict controls, only by authorized individuals, and in compliance with data protection policies and regulations. Organizations should carefully weigh the benefits and risks of unmasking, based on their specific use cases and security requirements.



