Token-based data masking is a powerful technique that enables users to customize the masking of sensitive data according to their specific requirements. In this blog post, we will explore how to use token-based data masking with Protecto.ai. We’ll cover the endpoint, request method, payload, response, advantages, and various customization options available.
Endpoint and Authentication:
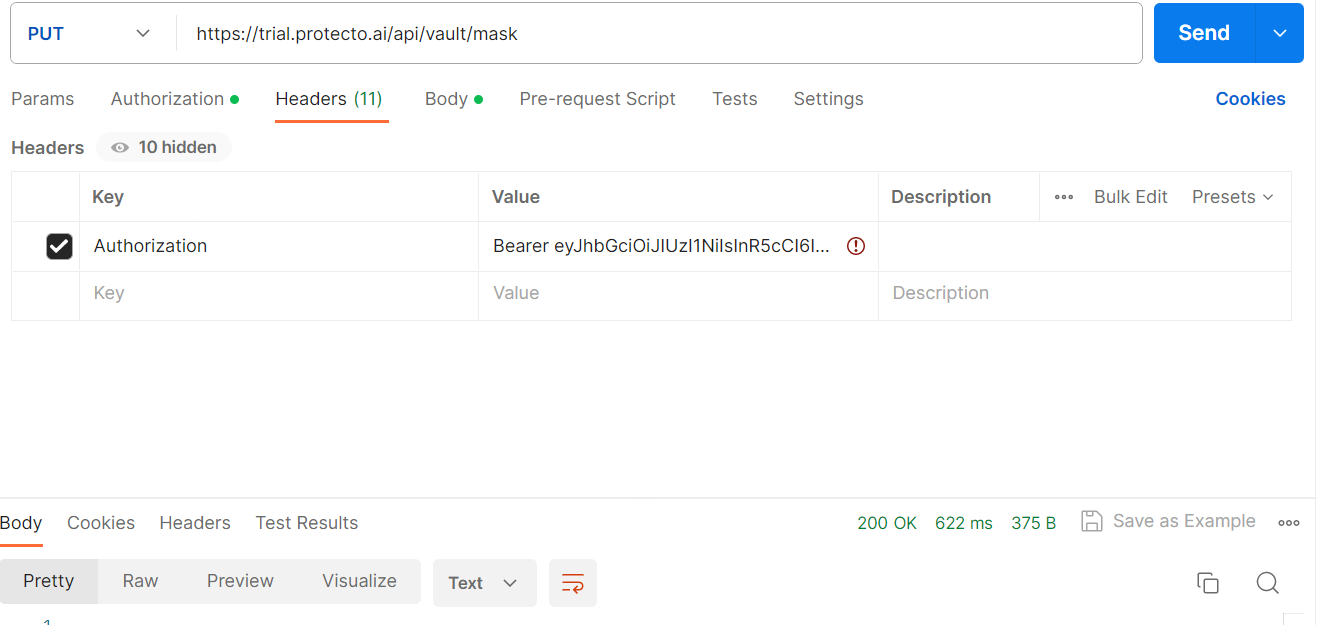
To use Protecto.ai’s token-based masking, you need to send a PUT request to the following endpoint:
Endpoint: https://trial.protecto.ai/api/vault/mask
For authentication, include the following token in the request headers:
Headers: {“Authorization”: “Bearer <AUTH_TOKEN>”}
Request Payload:
Here’s an example of a request payload to mask sensitive data with tokenName.
Request Payload:
{"mask": [{ "value": "George Williams", "token_name": "Numeric Token"}]}
Parameters for the Request Payload:
- value (string): The sensitive data value to be masked.
- token_name (string): The token to be used for masking the sensitive data.
Response:
Upon successful masking, you will receive a response with the masked data. Here’s an example of a response:
Response:
{"data": [{"value": "George Williams", "token_value": "2333", "token_name": "Numeric Token"}]}
Response Parameters:
- token_value (string): The generated token that replaces the sensitive data.
Advantage :
Token-based masking offers several advantages for data protection:
- Customization: Users can customize the masking of sensitive data according to their specific needs and preferences.
- Token Types:Users can choose from various token types, such as text-based tokens, alphanumeric tokens, or a combination of both, to match the context of the data being masked.
- Token Length:Users have the flexibility to define the desired length of the tokens. For example, tokens can be set to a specific number of characters or digits, ensuring they fit the data format.
- Case Sensitivity: can opt for case-sensitive or case-insensitive masking, allowing for precise control over how the data is obscured.